UEBA-Powered Tool for Security Investigations
Conduct prompt and thorough investigations on security incidents with multiple logs capturing every user action. Prevent insider threats with actionable insights based on advanced user and entity behavior analytics.

Scheduled Reports
Configure and schedule security and productivity reports for supervisors to always keep their finger on the pulse.
Immutable Audit Trail
The app maintains forensic-level logs recording every user action in the system to respond to compliance audits and ensure thorough security investigations.
Actionable Behavioral Insights
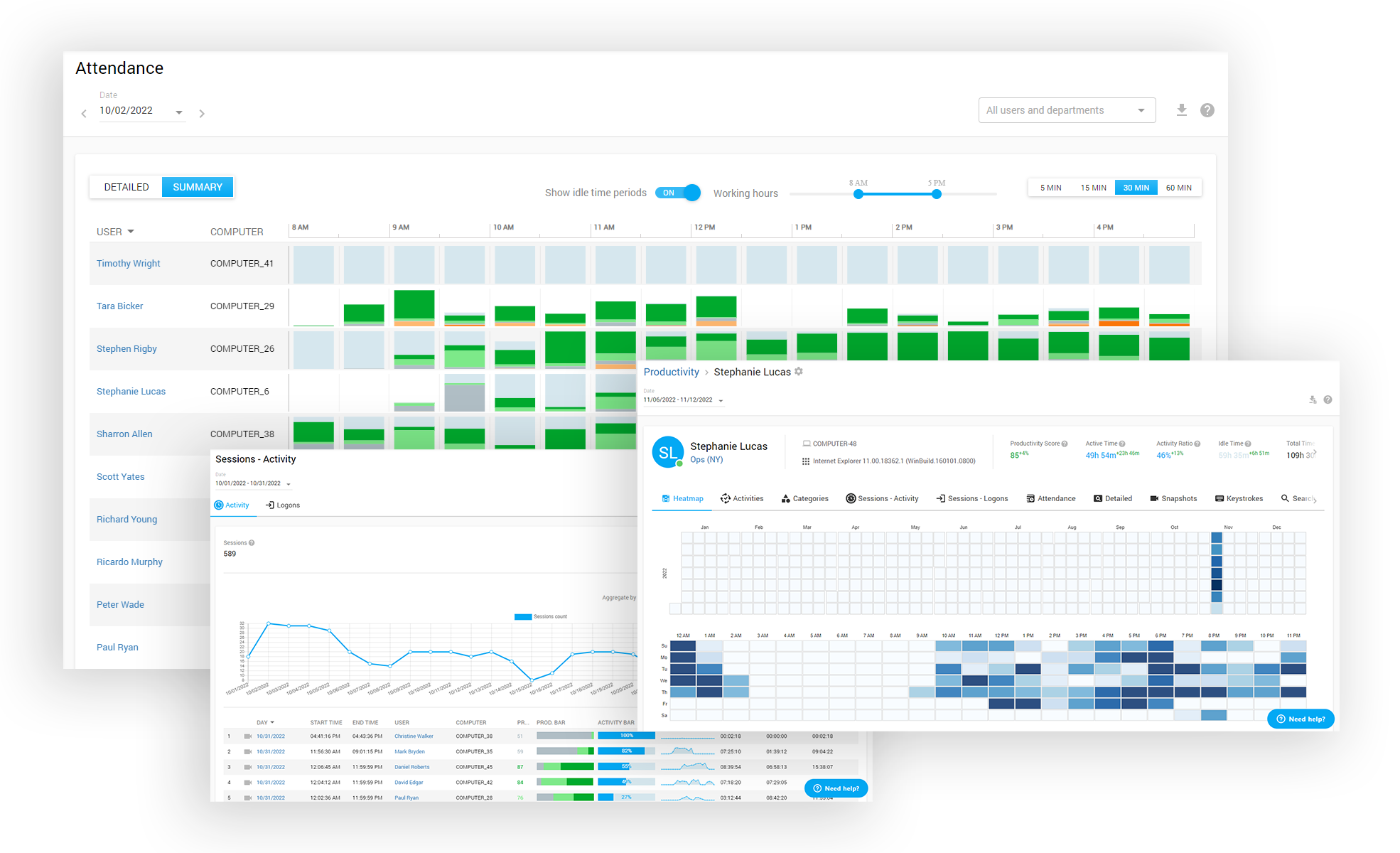
The app delivers reliable statistics and easy-to-grasp visualizations to spot productivity patterns and role models for creating a performance-boosting environment.
How Controlio builds a forensic evidence
base and helps companies strengthen cybersecurity
Detect improper employee behavior and protect your company’s data and assets from negligent or malicious insiders with Controlio’s smart algorithms and automated incident response features.





What Are Controlio Features?





Departments hierarchy
Live sessions monitoring
Remote client agent deployment
Multi-login Dashboard with access control list
Data Export to PDF, CSV
Agent Stealth mode and Icon mode
Audit Log (tracks activities inside the Dashboard)
2-Step Authentication
Cloud-based, on-premises, private AWS cloud deployment options
GDPR data recording&view mode
API for data integration
Active Directory OUs and users synchronization
Reviews
What our customers are saying
“EFFECTIVE DATA MONITORING, INSIGHTS AND ANALYSIS”

"I like the option set 'do not track' for specific users and flexibility to adjust licensing for data collection. Also the ability to group users for analyzing productivity at the group, company, or individual level is incredibly beneficial."
April 20, 2025
Senior Project Manager, Medical Devices, 51-1000 employeesUsed the software for: 6-12 months
“IMPROVES PRODUCTIVITY BY A HUGE MARGIN”

"Tracking accurate times for any app that was difficult before and it doesn't slow down our systems and the alerts for unauthorized access keep our data secure."
July 23, 2025
Marketing Specialist, Marketing and advertising, 11-50 employeesUsed the software for 1-5 months
“THE BEST TIME TRACKING SOFTWARE”

"It is incredibly user-friendly, you can download it quickly and access excellent customer support for any issues encountered."
May 24, 2025
Group IT Director, Transportation/Trucking/Railroad, 51-1000 employeesUsed the software for 1-2 years






